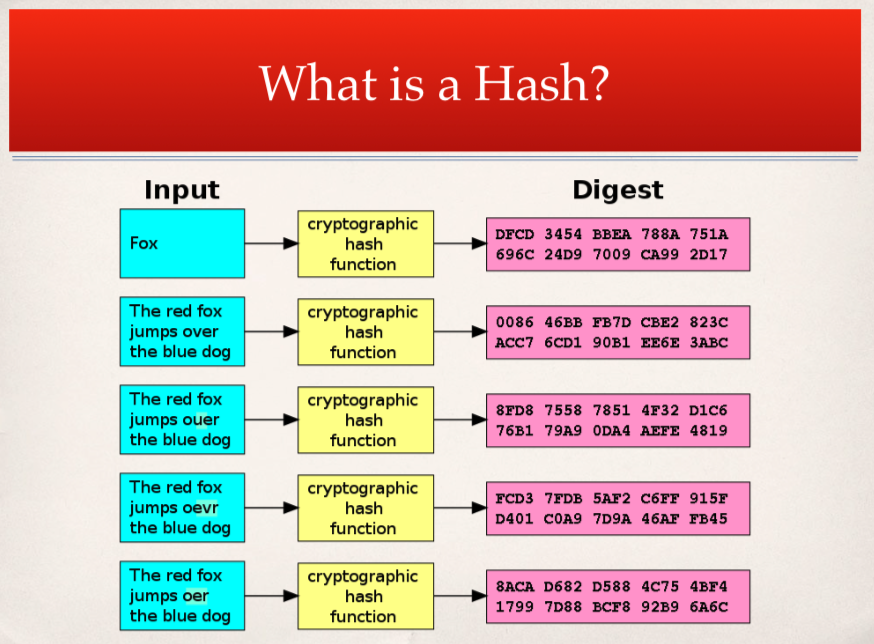
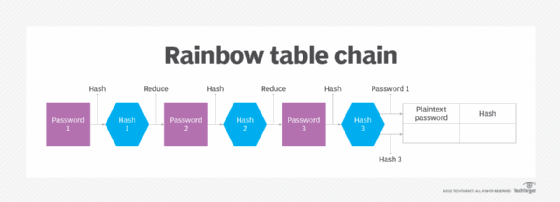
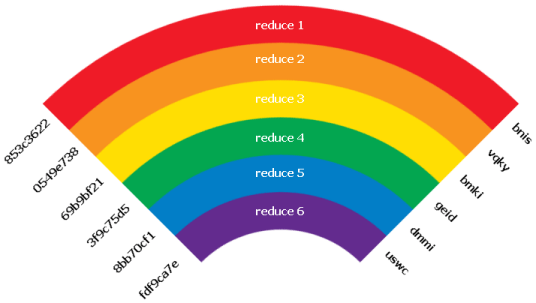
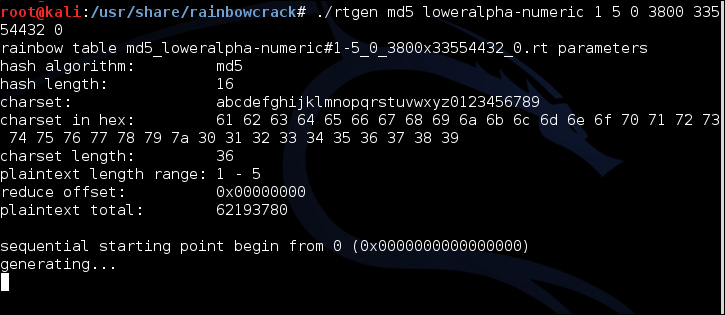
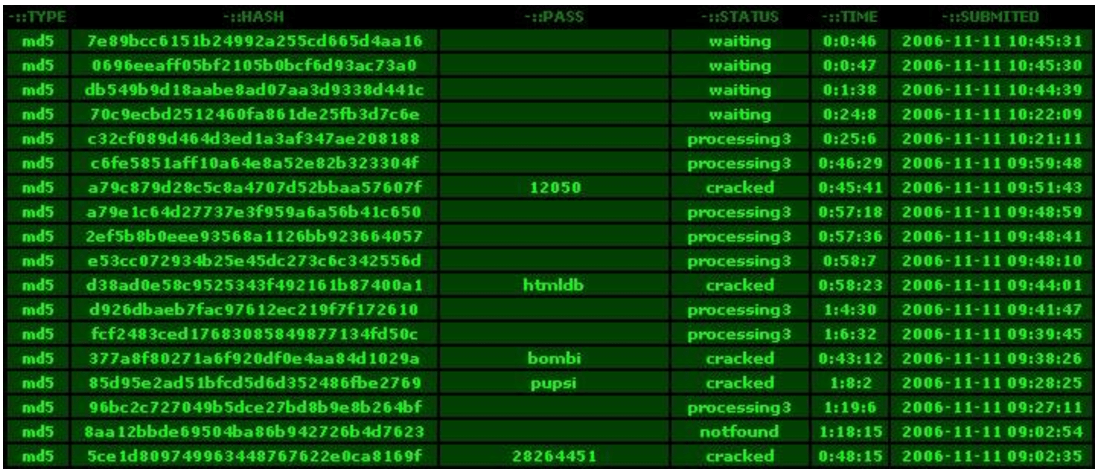
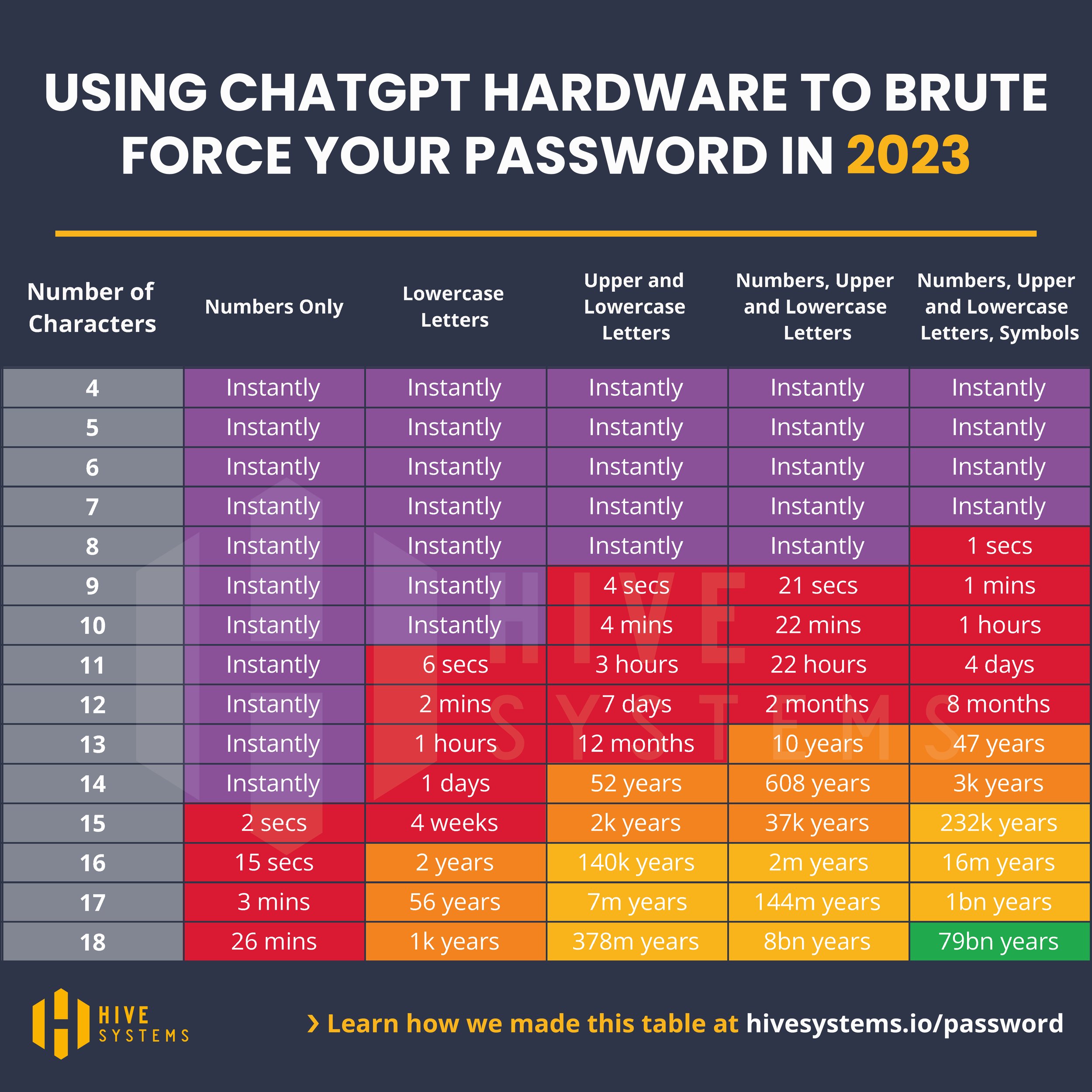
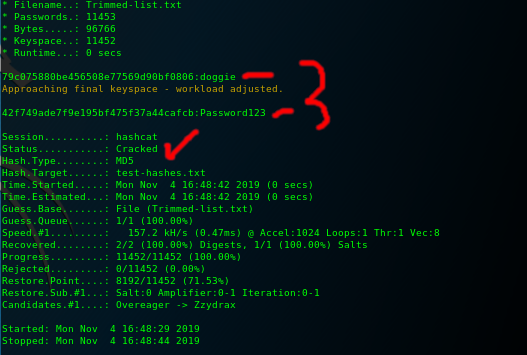
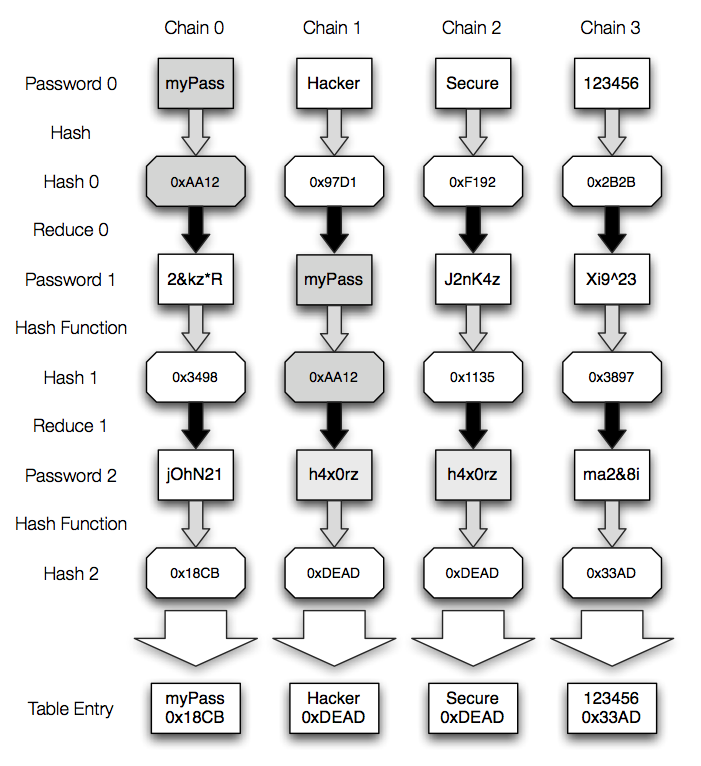
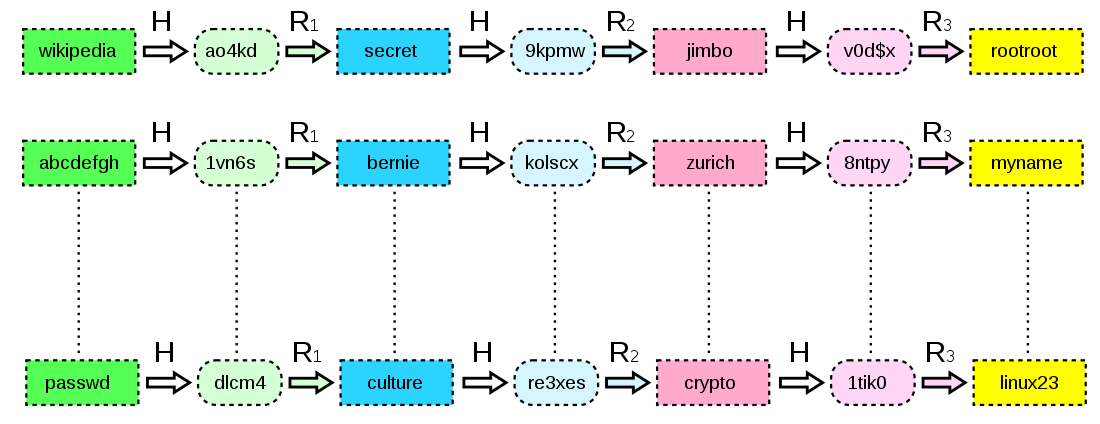
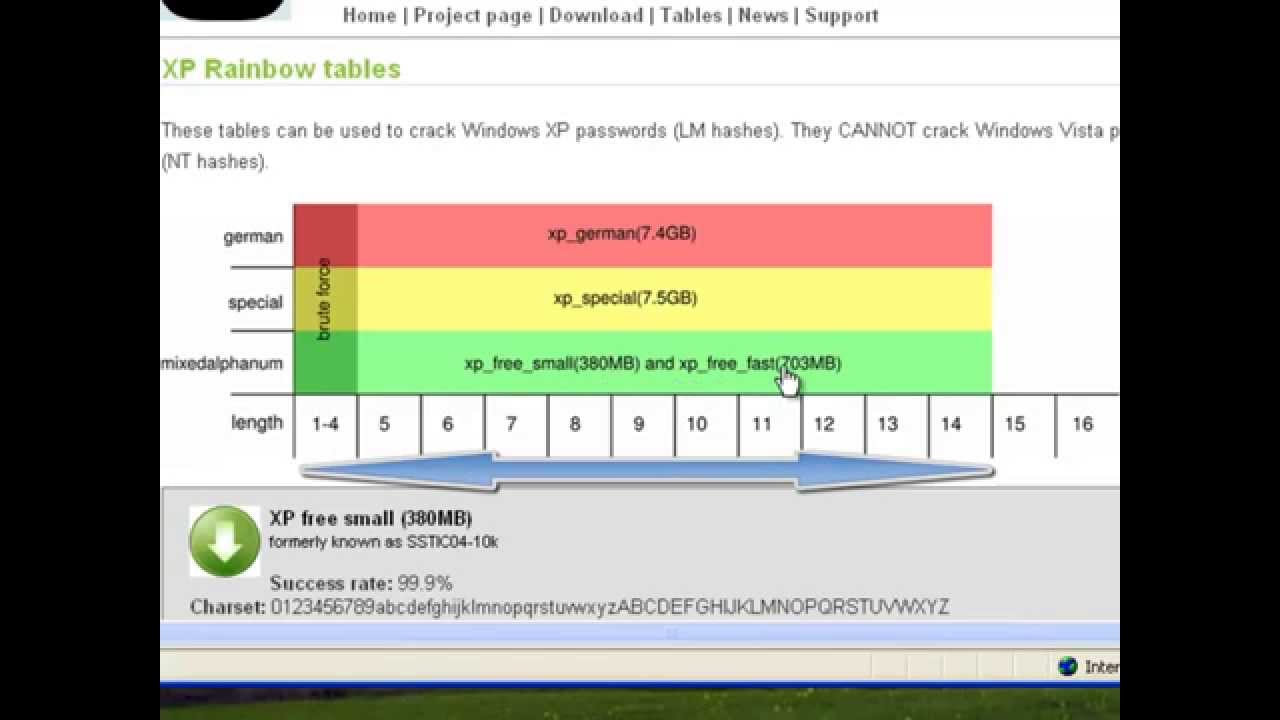
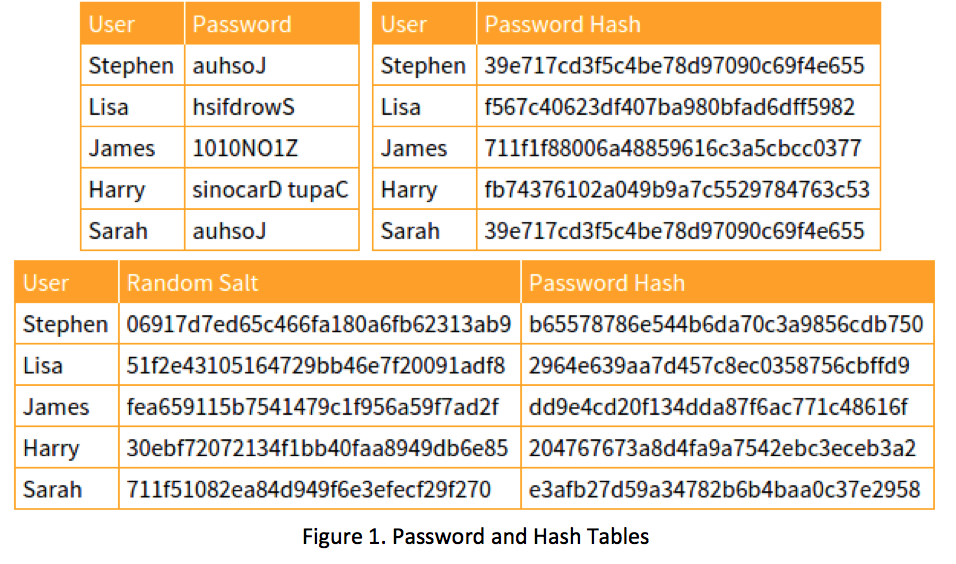
I͛P͛h͛o͛n͛e͛G͛a͛l͛a͛x͛y͛M͛D͛ 11K͛ 🏴☠️ on Twitter: "Rainbow table attack #attack #attacks #cyber #cybersecurity #cyberattack #hash #table #hashing #hac #hacks #hack #hacker #hacked #hacker #hackers #hacking #ddos #awareness #aware #safe #security ...